 I got to confess that I am a big podcast fan and one I am fond of is PaulDotCom – Security Weekly (I also hear it while I am jogging) So when I read in the blog the Mark Baggett’s post: Capturing SSH V1 & V2 Credentials with a MitM ssh honeypot I just feel like “I have to try it”. So I did and wrote this presentation for Sm4rt Security Services’ Tech Day, but I wanted to go further so I wrote it in a way that can be useful for the Pentesters and the Information Security Officers in the company.
I got to confess that I am a big podcast fan and one I am fond of is PaulDotCom – Security Weekly (I also hear it while I am jogging) So when I read in the blog the Mark Baggett’s post: Capturing SSH V1 & V2 Credentials with a MitM ssh honeypot I just feel like “I have to try it”. So I did and wrote this presentation for Sm4rt Security Services’ Tech Day, but I wanted to go further so I wrote it in a way that can be useful for the Pentesters and the Information Security Officers in the company.
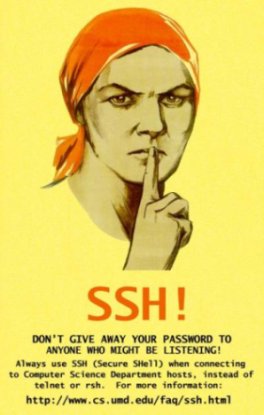
In the first part I talk about some basic concepts about SSH then I got for the hacking part so I give a demonstration based on the Mark Baggett’s post and I finish giving come SSH security tips based on my experience and some articles I found on Internet. I hope you found it interesting.
You can download it from here:
SSH Hacking and Good.Practices by Adrian Puente Z. (PDF Presentation)
Please visit my other Hacking Projects o Security Articles.
If you have something valuable to add to this presentation, please leave your comment.
References:
- Secure Shell from Wikipedia, the free encyclopedia
- Red Hat Linux 9: Red Hat Linux Reference Guide, Chapter 18. SSH Protocol
- Capturing SSH V1 & V2 Credentials with a MitM ssh honeypot by Mark Baggett
- Top 20 OpenSSH Server Best Security Practices
- Key-Based SSH Logins With PuTTY
Adrián Puente Z.
Technorati Tags:
Adrian Puente Z. hackarandas SSH hacking Man in the Middle Best Practices Security





Pingback: H4CKarandas » Blog Archive » RT @hackarandas: SSH Hacking a…
Pingback: Tweets that mention H4CKarandas » Blog Archive » SSH Hacking and Good Practices -- Topsy.com